
The Dutch National Coordinator for Security and Counterterrorism (NCTV) has released its annual cybersecurity assessment for 2025 under the theme "A Risky Mix in an Unpredictable World." The report documents a year in which state-sponsored attackers, cybercriminals and hacktivists operated in increasingly overlapping ways — making threat attribution harder and the impact on businesses and public services more severe. This report distils the key findings for IT and security professionals and business leaders operating in the Netherlands and broader Europe.
1. What Happened: Major Incidents in 2025
1-1. State-Sponsored Attacks Reach Dutch Soil
In 2025, state-sponsored cyber operations were no longer a distant concern — they caused direct, documented damage inside the Netherlands.- Russia: The newly identified 'Laundry Bear' group executed a cyberattack against the Dutch National Police. Russian actors also carried out the first confirmed cyber sabotage against digital control systems of Dutch public infrastructure in 2024, a trend that continued in 2025.
- China: The 'Salt Typhoon' group, known for long-term intrusions into US telecoms, was also found to have compromised routers at small Dutch internet service providers.
- North Korea: The 'Famous Chollima' group stole approximately $1.5 billion in cryptocurrency — the largest theft of its kind — with Dutch companies among the targets. In 40% of cases, the group used insider tactics, posing as freelance IT workers.
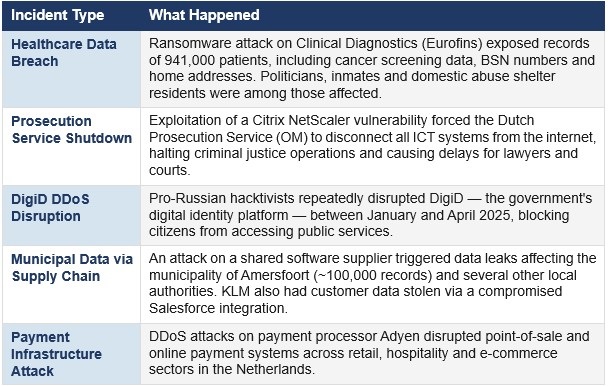
1-2. Notable Incidents at a Glance
Why It Matters: Three Structural Risks
2-1. Edge Devices Are the Primary Entry Point
Firewalls, VPN gateways and routers — collectively referred to as 'edge devices' — remain the most frequently exploited entry point for attackers. MIVD has warned that vulnerabilities in these devices are being actively exploited within hours to days of public disclosure, often before organisations have time to patch.Recent incidents further reinforce this trend. Citrix NetScaler, FortiManager and Microsoft SharePoint vulnerabilities were all confirmed to have been exploited before their public disclosure (zero-day attacks). This demonstrates that patch management alone is no longer a sufficient defence strategy.
2-2. Generative AI Is Lowering the Bar for Attackers
The rapid adoption of generative AI tools has amplified existing threats by enabling less technically skilled actors to conduct sophisticated attacks. Documented uses in 2025 include:- Highly convincing spear-phishing emails generated in multiple languages
- Assisted malware code development
- Automated scanning for vulnerable systems
2-3. Supply Chain Concentration Creates Systemic Risk
The pattern of a single software or cloud provider being compromised and cascading into dozens of downstream victims was observed repeatedly in 2024–2025. CSAN refers to this as 'digital monoculture' risk — excessive dependence on a small number of large technology vendors creates single points of failure.The CrowdStrike update failure in July 2024 impacted Dutch government agencies and Schiphol Airport — a reminder that even non-malicious events in the supply chain can cause widespread operational disruption.
Outlook: What to Expect in 2026
3-1. Compounding Threats Will Intensify
NCTV assesses that the trends documented in CSAN 2025 will continue to accelerate. Pre-positioned access by state actors — particularly China's Volt Typhoon and Salt Typhoon — within Western critical infrastructure is already confirmed, and the risk of that access being activated for sabotage during a geopolitical crisis is rising. European organisations should assume this risk extends to their sector.3-2. AI-Enabled Attacks Will Mature
While generative AI in 2025 primarily amplified existing threats, 2026 is expected to see more autonomous AI-driven attack capabilities emerge — including AI systems that independently identify and exploit vulnerabilities. AI systems themselves are also becoming targets: training data poisoning and model manipulation are emerging as new defensive challenges.3-3. NIS2 / Cbw Compliance Becomes Operational
The Netherlands' implementation of the NIS2 Directive — the Cybersecurity Act (Cyberbeveiligingswet, Cbw) — will move into active enforcement. Organisations in sectors including telecoms, energy, finance, healthcare and transport will face stricter security requirements, mandatory incident reporting timelines and supply chain due diligence obligations. Businesses operating in the Netherlands should verify their classification under Cbw and begin gap assessments now.ID Europe’s Perspective
At ID Europe, we work with businesses across the Netherlands every day. What CSAN 2025 confirms is something we hear from clients regularly: the question is no longer whether your organisation will face a cyber threat, but whether you'll be ready when it happens. The window to get the basics right is now — before regulation tightens and threats multiply. ID Europe helps organisations navigate exactly these challenges — from vulnerability assessments to NIS2 readiness.This article is based on the Cybersecurity Assessment Netherlands 2025 (CSAN 2025) published by NCTV, November 2025.
If you have any questions about this article or are interested in the solutions mentioned above, please contact us via the link below.
Contact | ID Europe B.V. (idnet.co.jp)



